Privacy
- Proton Mail Discloses User Data Leading to Arrest in Spainrestoreprivacy.com Proton Mail Discloses User Data Leading to Arrest in Spain
Proton Mail came under scrutiny for its role in a legal request by the Spanish authorities leading to the identification and arrest of a user.

- Telegram founder and CEO alledges signal has backdoors, they don't provide reproduceible builds, etc.
Here's what he said in a post on his telegram channel:
> 🤫 A story shared by Jack Dorsey, the founder of Twitter, uncovered that the current leaders of Signal, an allegedly “secure” messaging app, are activists used by the US state department for regime change abroad 🥷
> 🥸 The US government spent $3M to build Signal’s encryption, and today the exact same encryption is implemented in WhatsApp, Facebook Messenger, Google Messages and even Skype. It looks almost as if big tech in the US is not allowed to build its own encryption protocols that would be independent of government interference 🐕🦺
> 🕵️♂️ An alarming number of important people I’ve spoken to remarked that their “private” Signal messages had been exploited against them in US courts or media. But whenever somebody raises doubt about their encryption, Signal’s typical response is “we are open source so anyone can verify that everything is all right”. That, however, is a trick 🤡
> 🕵️♂️ Unlike Telegram, Signal doesn’t allow researchers to make sure that their GitHub code is the same code that is used in the Signal app run on users’ iPhones. Signal refused to add reproducible builds for iOS, closing a GitHub request from the community. And WhatsApp doesn’t even publish the code of its apps, so all their talk about “privacy” is an even more obvious circus trick 💤
> 🛡 Telegram is the only massively popular messaging service that allows everyone to make sure that all of its apps indeed use the same open source code that is published on Github. For the past ten years, Telegram Secret Chats have remained the only popular method of communication that is verifiably private 💪
Original post: https://t.me/durov/274
- Privacy.com alternative for the UK & EU region
Recently I just hit by stolen card detail and makes me searching a virtual card service. Anyone knows any works in the UK and EU region? Apparently Privacy.com needs SSN to work now. Thanks.
- Smart meter data: the Government’s at it againwww.openrightsgroup.org Smart meter data: the Government’s at it again
Back in October 2022, ORG exposed Government plans to snoop on UK residents’ smart meters and energy consumption data.

- 12 ft ladder Alternative?
12ft ladder doesnt seem to work anymore, on major sites at least. Does anyone have an alternative? Gracias
- What email provider do you use for sign ups?
I used to use Protonmail, however the verification steps become tedious when creating unique emails for sign ups. I've switched to Tutanota despite it contravening their one account policy. What do you all use for one off emails (for sign ups etc )? Or do you prefer one of those 10 minute email sites?
- Materialious - Desktop & Android clientmaterialio.us Materialious - Modern material design for Invidious
Modern material design for Invidious.
Materialious now can be used as a Desktop or Android application. Allowing it to be used for any Invidious instance!
https://github.com/Materialious/Materialious/tree/main?tab=readme-ov-file
- Thoughts on Google turning every device into a scanner for Find My Device?
Received notice of a change to the service in my inbox today. Seems icky to me.
> Devices in the network use Bluetooth to scan for nearby items. If other devices detect your items, they’ll securely send the locations where the items were detected to Find My Device. Your Android devices will do the same to help others find their offline items when detected nearby
> Your devices’ locations will be encrypted using the PIN, pattern, or password for your Android devices. They can only be seen by you and those you share your devices with in Find My Device. They will not be visible to Google or used for other purposes.
- sharing my simple wireguard kill-switch for Linux
cross-posted from: https://lemmings.world/post/8926396
> In light of the recent TunnelVision vulnerability I wanted to share a simple firewall that I wrote for wireguard VPNs. > > https://codeberg.org/xabadak/wg-lockdown > > If you use a fancy official VPN client from Mullvad, PIA, etc, you won't need this since most clients already have a kill switch built in (also called Lockdown Mode in Mullvad). This is if you use a barebones wireguard VPN like me, or if your VPN client has a poorly-designed kill switch (like NordVPN, more info here). > > A firewall should mitigate the vulnerability, though it does create a side-channel that can be exploited in extremely unlikely circumstances, so a better solution would be to use network namespaces (more info here). Unfortunately I'm a noob and I couldn't find any scripts or tools to do it that way.
- Man Booked For Using VPN In J&K's Rajouri, 3rd Such Case In 2 Dayswww.ndtv.com Man Booked For Using VPN In J&K's Rajouri, 3rd Such Case In 2 Days
A man in Rajouri district was booked on Tuesday for using virtual private network (VPN) which was banned last month by the district administration, officials said.

cross-posted from: https://lemmy.world/post/15187027
> cross-posted from: https://lemmy.world/post/15187023
- Novel attack against virtually all VPN apps neuters their entire purposearstechnica.com Novel attack against virtually all VPN apps neuters their entire purpose
TunnelVision vulnerability has existed since 2002 and may already be known to attackers.

Pulling this off requires high privileges in the network, so if this is done by intruder you're probably having a Really Bad Day anyway, but might be good to know if you're connecting to untrusted networks (public wifi etc). For now, if you need to be sure, either tether to Android - since the Android stack doesn't implement DHCP option 121 or run VPN in VM that isn't bridged.
- It's a long road back to privacy
This post will be my personal experience about trying to gain back my privacy after years of being privacy unconscious. And foremost I want to apologize for my English, if it isn't perfect, 'cause English is not my first language.
I was already using Linux for the past year. I tried switching to it three times, and only the third time was successful. Also interested in open source I was for quite a long time, but the privacy topic has never really interested me. I was following this stupid statement: «I don't worry about privacy because I have nothing to hide», which I regret now. But last Christmas, I suddenly realized how much data I was giving away to Big Tech (and not only them). I can't perfectly remember what did lead me to that realization. Was it some YouTube video, privacy policy that I suddenly decided to check out or something else, but I immediately started to action.
For the past 6 months I deleted more than 100 accounts. Sometimes it was as easy as to press the button, sometimes I had to email support, and sometimes I literally had to fight for my right to remove the account. Even today there are still 7 accounts left, that I can not delete either because support is ignoring me, or because the process is too slow, or because the service simply does not give the right to remove user account. JustDeleteMe actually helped me very much with that process, and I've even contributed to the project a few times, so to the other users who'll follow my way the process would be at least a little easier.
Today is a special day, though, because I finally get rid of my Google and Microsoft accounts. I can finally breathe free. My situation is still not perfect, 'cause I still have some proprietary, privacy invasive accounts left, like Steam, Discord, or my banking apps. I can't just immediately drop them, but at least I've reduced the amount of information I left behind. What's the moral? Welp, it would be so much easier for today's me if yesterday's me had been concerned about privacy in the first place.
- Why Your VPN May Not Be As Secure As It Claims
> Virtual private networking (VPN) companies market their services as a way to prevent anyone from snooping on your Internet usage. But new research suggests this is a dangerous assumption when connecting to a VPN via an untrusted network, because attackers on the same network could force a target’s traffic off of the protection provided by their VPN without triggering any alerts to the user.
- Mullvad VPN: Introducing Defense against AI-guided Traffic Analysis (DAITA)mullvad.net Introducing Defense against AI-guided Traffic Analysis (DAITA) | Mullvad VPN
Even if you have encrypted your traffic with a VPN (or the Tor Network), advanced traffic analysis is a growing threat against your privacy. Therefore, we now introduce DAITA.

>Even if you have encrypted your traffic with a VPN (or the Tor Network), advanced traffic analysis is a growing threat against your privacy. Therefore, we now introduce DAITA.
>Through constant packet sizes, random background traffic and data pattern distortion we are taking the first step in our battle against sophisticated traffic analysis.
- Why every TOTP app default uses SHA-1 hash encryption?
I use Aegis as my 2fa. Today on new token creation I observed that there's hash function set to SHA-1, later checked all my tokens and the result is same type of encryption used for all. So I have edited all my tokens to SHA-256 as a result my totp doesn't authenticate. Do I have to rescan my tokens for updating to SHA-256 or it doesn't work like that?
Security: SHA-1 < SHA-256 < SHA-512
Speed: SHA-1 > SHA-256 > SHA-512
My doubts are: Why can't we use SHA-256? Is it because TOTP requires less time so faster one(SHA-1) is chosen? Can we use SHA-256 for TOTPs?
- Why people don't talk about Google Maps' privacy issues
YouTube Video
Click to view this content.
Title is editorialized because the original is, frankly, clickbait garbage
- [Question] Securely Passing Host VPN to KVM?
I've attempted to create a VM on my ubuntu host machine that is accessing the internet via a dedicated VPN app. I'm able to disconnect my host VPN and access the web within the VM, but cannot access the web when the host VPN is enabled. Ideally I'd like to enable the VPN on the host and pass through web access to the VM.
I have two questions:
- If my use case is to use a VM to increase privacy and security as well as isolate my operations within the VM from my host, is it better to have the VPN app from inside the VM or pass the host's through to the VM?
- If it doesn't make much of a difference, how can I go about passing the host's VPN to the VM?
In either scenario, I'd still like to keep the host's VPN active while being able to use the VM, which I currently cannot.
- Need help figuring out bookmark management
Over the years I have saved many bookmarks in Firefox in various folders for interesting, useful or just frequently used websites.
Now I've recently moved a lot of stuff to more private (foss/selfhosted) alternative and I'm considering moving browsers too. Since the bookmarks are so integrated into the browser I was wondering what you guys do/recommend in order to keep a bit more freedom.
One option I could think of would be to write them into a Markdown doc and to sync it with all the other notes I keep but that's a bit inconvenient - there's got to be a nicer way that doesn't send every action to a browser corpo, right?
- End-to-end encryption may be the bane of cops, but they can't close that Pandora's Boxwww.theregister.com Cop complaints won't stop E2EE, says encryption advocate
Internet Society's Robin Wilton tells us the war on privacy won't be won by the plod

- HDMI stream live processing?
I’m getting tired of the extremely loud ads on that don’t seem to be subject to the old TV broadcasting laws that prevent them from being blasted 10db louder than the actual content. Wondering if there’s stuff out there that would let me take the hdmi stream from my Apple TV or other streaming source, and do ad detection like the olden days so that it could just mute or do volume leveling at least.
I suppose something very basic might just be an hdmi splitter to a rpi with hdmi that’ll detect ads via the black screens or “this ad will over over in 30s” overlays, then send a mute signal over CEC or something to a receiver or TV….but would be nice if it could modify the hdmi signal directly.
Thoughts on what to search for to do something like this?
- Is Instander dead?
Hi, I used to use Instander to browse Instagram privately but it doesn't seem to be updated anymore, is there an alternative that you recommend that has similar features? Like "ghost mode" when watching stories
- "Everything being a sleek App, instead of being a clunky website. Which is definitely the way to go." - Mrwhosetheboss
(timestamp-link) iPad Pro M4 Hands on - Why I just bought it. Review from a top YT reviewer, Mrwhosetheboss. How do you guys feel about it?
- How Do I Prepare My Phone for a Protest?themarkup.org How Do I Prepare My Phone for a Protest? (Updated 2024) – The Markup
Simple steps to take before hitting the streets

> Simple steps to take before hitting the streets
- Disable VPN while browsing casual or leave running?
Hey guys n gurls, I was wondering if it is smart to disable my VPN connection for casual browsing.
Reasons: when having VPN constantly running it may be possible to track me via browser fingerprinting.
Szenario: the connection coming from the VPN which hypothetically downloaded a torrent, tries to watch capitalist propaganda while living in China, etc.pp has this screen ratio, this locale, this addons etc. And (more important) the YouTube login cookie we know belongs to this physical person/telephone number etc.
So I am wondering if I should only use the VPN when "needing" it (read articles not available in country, Netflix, read information government doesn't like, things like that.) Or if I'm missing something here and I could obscure my causal day to day browsing as well without decreasing the security of the VPN.
For reference, the VPN doesn't log anything (for more than a day) to my knowledge
EDIT: From what I understand from the comments: switching the VPN has little to no impact on widely used tracking and if at all makes it easier to corelate data. People emphasize the general lack of full privacy if you are wanted by entities willing to spend enough resources. But for the general need of privacy in normal usecases it makes more sense to just leave the VPN running.
- The Best Secure Email Providers in 2024blog.thenewoil.org The Best Secure Email Providers in 2024
Like it or not, email is a critical part of our digital lives. It’s how we sign up for accounts, get notifications, and communicate with ...

> Like it or not, email is a critical part of our digital lives. It’s how we sign up for accounts, get notifications, and communicate with a wide range of entities online. Critics of email rightfully point out that email suffers from a significant number of flaws that make it less than ideal, but that doesn’t change the current reality. In light of that reality, I believe that an encrypted email provider is a must-have for everyone in today’s age of rampant data breaches, insider threats, warrantless police access, and targeted advertising. If I can get access to your emails, I can get a range of sensitive information including where you bank (to craft more convincing phishing attacks), information about pets (I get notifications each year from the vet for my cats’ annual checkups), calendar reminders, news announcements from family, support tickets from services you use, and more. In a worse case scenario, if I get access to the account itself, it’s trivial to simply issue password reset requests for nearly any of those accounts, have it to sent to said compromised email account, and gain access to a wide number of other accounts you use – from banking to shopping and more – for any number of reasons. So this week, let’s look into the top encrypted email providers The New Oil recommends and their features to help decide which one is right for you.
- DNS traffic can leak outside the VPN tunnel on Androidmullvad.net DNS traffic can leak outside the VPN tunnel on Android
We were recently made aware of multiple potential DNS leaks on Android. They stem from bugs in Android itself, and only affect certain apps.

- What VPN are you using?
I use Proton. But I continue to run into more and more websites and services that detect my VPN and refuse my connection, or just run literally 40 captchas in a row until I just give up.
I use Proton because it has a "suite" of products under a single subscription, but that benefit is losing it's allure as some of their products are pretty shitty from a user experience perspective, their customer support is atrocious, and they don't seem to pay any attention to what their users actually want.
Does anyone track known VPN servers? Is there a specific provider that causes less problems? Does anyone test different VPNs for detection?
Thinking about cancelling my subscription and moving to Mullvad.
- Trying to understand Consent Forms, Cookies and Third-Party Vendors
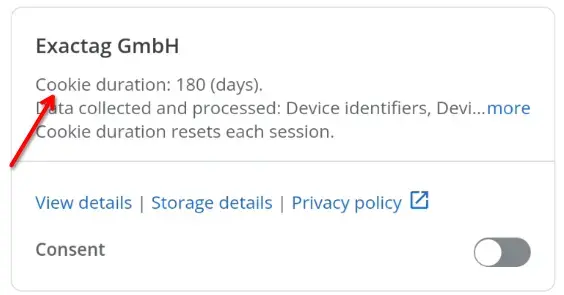
Yo peeps, I'm currently looking into TCF Vendors, Ad partners and their whole corporate greed hellhole of tracking. I am writing a paper on this, and would like for everything to be factually correct. However, I am struggling to understand one particular part of this "transparency framework" and hope someone can help me clarify on cookie-duration.
As seen in the first thumbnail, the cookie duration is listed as 180 days. However, upon selecting > Storage Details, each cookie is displayed in further detail. In this detailed section, there are additional cookies with duration as high as 1825 days, not 180... So which is it? Currently, I'm (obviously) assuming the worst, as in, it being 1825 and not 180 days. There are additional cookies on this list, see spoiler below, that have cookies with the duration of 180 days. Why are the cookies with the highest duration listed on the first page? And if the answer is that "it would look worse", then they also have cookies with lower amount of days than 180 that could have been used. There are multiple cookies with different durations, do all of them count?
If needed here is a spolier that includes all the cookies in detail from the Exactag GmbH vendor.
SPOILER
``` Exactag GmbH - Storage details
Name: exactag_new_adoptout Type: Cookie Duration: 1825 (days) Domain: Purposes: Store and/or access information on a device Refreshes Cookies: No
Name: exactag_new_ccoptout Type: Cookie Duration: 1825 (days) Domain: Purposes: Store and/or access information on a device Refreshes Cookies: No
Name: exactag_new_optout Type: Cookie Duration: 1825 (days) Domain: Purposes: Store and/or access information on a device Refreshes Cookies: No
Name: exactag_new_cpv Type: Cookie Duration: 1 (days) Domain: Purposes: Store and/or access information on a device Measure advertising performance Measure content performance Refreshes Cookies: No
Name: exactag_new_gk Type: Cookie Duration: 60 (days) Domain: Purposes: Store and/or access information on a device Measure advertising performance Measure content performance Refreshes Cookies: No
Name: exactag_new_uk Type: Cookie Duration: 180 (days) Domain: Purposes: Store and/or access information on a device Measure advertising performance Measure content performance Refreshes Cookies: Yes
Name: exactag_new_user Type: Cookie Duration: 180 (days) Domain: Purposes: Store and/or access information on a device Measure advertising performance Measure content performance Refreshes Cookies: Yes
Name: session_session Type: Cookie Duration: Uses session cookies Domain: Purposes: Store and/or access information on a device Measure advertising performance Measure content performance Refreshes Cookies: No ```
Let me know if any additional information is needed.
- Microsoft plans to lock down Windows DNS like never before. Here’s how.arstechnica.com Microsoft plans to lock down Windows DNS like never before. Here’s how.
ZTDNS brings the best of both worlds to DNS: encryption and fine-grained control.

- Any web site that lets you share files with people like xender ?
I remember there being apps like xender, easy share etc. which lets you share files by one person activating hotspot and the other wifi you just have to have both party close to each other and they use no data . But they are all closed source and probably spyware and its too much of a hassle to get others to download a file sharing app from fdroid when you need to share big files so is there any website or web app which is private (completely offline after loading, is foss etc.). It also has to work on android and have good enough speed .
- What is your GoCryptFS/CryFS workflow for syncing (let's say) Nextcloud encrypted folders on Android?
I was using the Plasma Vaults feature for the first time on my Linux computer, and it worked nicely (GoCryptFS), but when I wanted to sync that folder on my Android... I just couldn't find the right tool on Android for the job.
How do you solve this problem yourself?
- US Police Banned by Microsoft from Using Azure's AI Facial Recognition Technologywww.techtimes.com US Police Banned by Microsoft from Using Azure's AI Facial Recognition Technology
Microsoft says US Police Departments cannot use Azure's AI-powered facial recognition technology.

- Number of email accounts for financials
Does it make sense to have separate emails for each individual financial account (banking, credit cards) or is that overkill? I'm just thinking that if a hacker got access to one email they'd have all account information?
- Any way to make forwarded notifications from my other user on GrapheneOS show the full contents of the notification?
When I get notification from my other user account (which is named "Work"), it only says "Notification from Teams for Work"
Teams = Microsoft Teams app
I just hate having to switch back and forth between accounts to see the full contents of the message. I really don't want Teams or Outlook installed on my main account, I want my main account to FOSS, while my other account can have the other proprietary apps. I just want to be able to see the full contents of the message when it gets forwarded, and not just "Notification".
- Creating dummy Google accounts
I use GrapheneOS ony phone and a Mac with the security options as optimized as possible. For most of my emailing etc, I use Tuta and Proton. There are instances however, where having a Google account is beneficial (some apps for example won't download from Aurora store in anonymous mode).
Is it advisable/possible to create a dummy Google account with minimal ID/credentials? And if so, what are some best practices for doing so?
Or, do I resign myself to the fact that with more control over my data, I have to sacrifice more?