YouTube Video
Click to view this content.
KeepassXC ++ Yubikey ++ STRONG password changed every 7 days.
Tap for spoiler
This solution is compatible with virtually all platforms & browsers
YouTube Video
Click to view this content.
The headline was bit sensationalist. So, I shortened it.
YouTube Video
Click to view this content.
> A video summary by Faan Rossouw of the Malware of the Day - XenoRAT///
> 🔗 Blog post located here: https://www.activecountermeasures.com/malware-of-the-day-xenorat/

YouTube Video
Click to view this content.
> Backdoor found in xz liblzma specifically targets the RSA implementation of OpenSSH. Story still developing.https://openwall.com/lists/oss-security/2024/03/2...
YouTube Video
Click to view this content.
AI summary of transcript:
> groundbreaking exploration into transmitting LoRaWAN signals via unconventional means—utilizing microcontrollers lacking native radio functionalities. By tweaking GPIO pins on devices like the CH32V203, ESP32-S2, and ESP8266, OP demonstrates how to generate RF signals strong enough to communicate with commercial LoRaWAN gateways and access the internet. This method deviates from traditional approaches that rely on specific radio chips or RF capabilities. The experiment not only surpasses expectations in terms of signal transmission distance but also showcases a novel blend of ingenuity and technical prowess. Through this project, the resilience and adaptability of LoRa technology are put on full display, proving its capability to facilitate long-range communications under inventive conditions. The venture into RF technology and signal generation through hardware manipulation opens new avenues for utilizing microcontrollers in ways previously deemed impractical, marking a significant achievement in the field.
With the small caveat that it will probably get me killed one day, my favorite tactic is blasting this and staring the guy down, expressionless, without breaking eye contact until he gets the hint.
The use of the AI buzzword raises some flags for me, personally.

YouTube Video
Click to view this content.
Hosky speaks at length about selective disclosure regimes using Midnight.
Privacy protocol closed devnet opens up soon.
YouTube Video
Click to view this content.
DO NOT try this EVER.
The feds will show up at your house and arrest you in less than 30 minutes.
Thanks. This was very good moderation. OP and I ended up becoming friendly. :)
YouTube Video
Click to view this content.
> Welcome to the Advanced Meshtastic Series. We'll be getting into some of the more advanced things you can do with Meshtastic.
YouTube Video
Click to view this content.
> Programs aren't capable of generating true random numbers, so how can we? Are they even useful? Dr Valerio Giuffrida demonstrates how to get a true random number from most computers.
I just learned about this podcast today. Enjoy!
As often as you desire! I’m so happy to see some content not posted by me on there. Thanks!
I’d humbly invite you to post it on https://infosec.pub/c/cypherpunk
It has been pretty quiet over there lately and I sincerely wish my small community had more activity.
Wake me up when they switch to RISC-V.
YouTube Video
Click to view this content.
In this talk we will discuss the radio jailbreaking journey that enabled us to perform the first public disclosure and security analysis of the proprietary cryptography used in TETRA (Terrestrial Trunked Radio): a European standard for trunked radio globally used by government agencies, police, prisons, emergency services and military operators. Besides governemental applications, TETRA is also widely deployed in industrial environments such as factory campuses, harbor container terminals and airports, as well as critical infrastructure such as SCADA telecontrol of oil rigs, pipelines, transportation and electric and water utilities. For over two decades, the underlying algorithms have remained secret and bound with restrictive NDAs prohibiting public scrutiny of this highly critical technology. As such, TETRA was one of the last bastions of widely deployed secret proprietary cryptography. We will discuss in detail how we managed to obtain the primitives and remain legally at liberty to publish our findings.
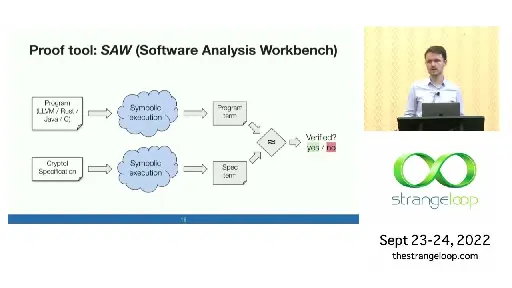
This is first in a series of blog posts on Formal Verification (FV).
> The motivation for Formal Verification > Security of smart contracts is still a crucial challenge: we all remember the DAO, parity hacks, a bunch of smaller attacks and the most recent delayed hard fork. We would like to see the future in which we can be way more confident about our code. > > Depending how you count, event over a half a billion dollars (by today’s Ethereum evaluation), was lost in a couple of biggest smart contract hacks. > > What about if behind every responsible piece of code stands pure solid mathematics instead of personal conviction of developers? With formal verification tools for Ethereum finally maturing, it is now not only possible but also practical. > > In this and following post we will be getting step by step into the world of K-framework, which allows to formally verify EVM smart contracts.

YouTube Video
Click to view this content.
YouTube Video
Click to view this content.
YouTube Video
Click to view this content.
> Spies used to meet in the park to exchange code words, now things have moved on - Robert Miles explains the principle of Public/Private Key Cryptography > > note1: Yes, it should have been 'Obi Wan' not 'Obi One' :) > note2: The string of 'garbage' text in the two examples should have been different to illustrate more clearly that there are two different systems in use.
YouTube Video
Click to view this content.
> Slides - https://authress.io/l/codemotion > > Conference: > Codemotion Madrid 2023 > https://talks.codemotion.com/why-you-...
Can someone recommend a more secure method? I've been told many times that using git for secret management would present a potential vulnerability.
Star Trek: The Next Generation
cyph3rPunk, for sure. ;)
The damned bot beat me to it. This is a great writeup.
I can’t speak for OP. But I, for one, do that because instances shut down all the time without a trace.
Fool me once: I had a solo account on aspiechattr.me and that instance disappeared randomly one day.
😂I wonder how many people here even get that reference (beside you and I).😂
Usually a reload does the trick. That’s a lemmy thing. Infosec.pub is rock solid and reliable.
I posted a link to legendary hardcore punk band, Dag Nasty. 🤘🏽