Pulse of Truth
- Companies spend more on cybersecurity but struggle to track expenseswww.helpnetsecurity.com Companies spend more on cybersecurity but struggle to track expenses - Help Net Security
Despite increasing budgets, only 36% of organizations have a formal approach to determining cybersecurity budgets.

Most companies do not know how effectively they are investing money to fight the cybersecurity threat, according to Optiv. Cybersecurity budgets are increasing and cyber incidents are rampant, and yet only a small percentage of respondents have a formal approach to determining cybersecurity budgets, which can lead to inefficiencies and missed opportunities to address critical security gaps. Lack of formal approach to cybersecurity budgets Based on an independent Ponemon Institute survey, the report reveals a … More → The post Companies spend more on cybersecurity but struggle to track expenses appeared first on Help Net Security.
- Almost Every Apple Device Vulnerable To CocoaPods Supply Chain Attackpacketstormsecurity.com 'Almost every Apple device' vulnerable to CocoaPods
Dependency manager used in millions of apps leaves a bitter taste

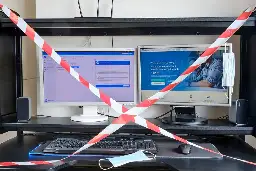
- Feds Hit Health Entity With $950K Fine in Ransomware Attackwww.bankinfosecurity.com Feds Hit Health Entity With $950K Fine in Ransomware Attack
The U.S. Department of Health and Human Services has hit a Pennsylvania-based healthcare system with a $950,000 settlement for potential HIPAA violations found

Settlement Is Another Signal of HHS OCR's Latest Enforcement PriorityThe U.S. Department of Health and Human Services has hit a Pennsylvania-based healthcare system with a $950,000 settlement for potential HIPAA violations found during an investigation into a 2017 ransomware attack. It's HHS' third HIPAA enforcement action in a ransomware case so far.
- Verizon slapped with $847m patent paymentwww.datacenterdynamics.com Verizon slapped with $847m patent payment
Texas jury found the carrier guilty of 5G and hotspot infringements

Texas jury found the carrier guilty of 5G and hotspot infringements
- Wise confirms impact from Evolve Bank breachwww.scmagazine.com Wise confirms impact from Evolve Bank breach
Global fintech and money transfer company Wise has confirmed the compromise of some of its customers' data as a result of the LockBit ransomware attack against U.S. banking-as-a-service provider Evolve Bank & Trust, with which it has shared USD account information between 2020 and 2023, TechCrunch r...

Global fintech and money transfer company Wise has confirmed the compromise of some of its customers' data as a result of the LockBit ransomware attack against U.S. banking-as-a-service provider Evolve Bank & Trust, with which it has shared USD account information between 2020 and 2023, TechCrunch reports.
- Splunk Patches High-Severity Vulnerabilities In Enterprise Productpacketstormsecurity.com Splunk Patches High-Severity Vulnerabilities in Enterprise Product
Splunk has patched multiple vulnerabilities in Splunk Enterprise, including high-severity remote code execution bugs.

- Affirm says cardholders impacted by Evolve Bank data breachwww.bleepingcomputer.com Affirm says cardholders impacted by Evolve Bank data breach
Buy now, pay later loan company Affirm is warning that holders of its payment cards had their personal information exposed due to a data breach at its third-party issuer, Evolve Bank & Trust (Evolve).

Buy now, pay later loan company Affirm is warning that holders of its payment cards had their personal information exposed due to a data breach at its third-party issuer, Evolve Bank & Trust (Evolve). [...]
- New InnoSetup Malware posing As MS Office Crack To Evade detection
A new malware strain disguised as cracks and commercial tools utilizes a just-in-time generation tactic, and upon a download request, a unique malware variant with the same functionalities is created for the user, which allows the malware to evade detection based on pre-compiled hashes.   The malware leverages an installer UI to delay malicious actions until […] The post New InnoSetup Malware posing As MS Office Crack To Evade detection appeared first on Cyber Security News.
- Brain Cipher Released Decryption Keys for Free, Apologies to Indonesia
The notorious hacking group Brain Cipher has released decryption keys for free, allowing victims to recover their encrypted data without paying a ransom. This unexpected move has left cybersecurity experts and affected organizations scrambling to understand the implications. "Is Your System Under Attack? Try Cynet XDR: Automated Detection & Response for Endpoints, Networks, & Users!"- Free […] The post Brain Cipher Released Decryption Keys for Free, Apologies to Indonesia appeared first on Cyber Security News.
- Meta’s ‘Pay or Consent’ Data Model Breaches EU Lawwww.infosecurity-magazine.com Meta’s ‘Pay or Consent’ Data Model Breaches EU Law
The EU Commission said Meta’s pay or consent model means users cannot freely consent to their personal data being collected for advertising purposes

The EU Commission said Meta’s pay or consent model means users cannot freely consent to their personal data being collected for advertising purposes
- Baddies hijack Korean ERP vendor's update systems to spew malwarego.theregister.com Korean ERP vendor's update systems subverted to spew malware
Notorious 'Andariel' crew takes a bite of HotCroissant backdoor for fresh attack

Notorious 'Andariel' crew takes a bite of HotCroissant backdoor for fresh attack A South Korean ERP vendor's product update server has been attacked and used to deliver malware instead of product updates, according to local infosec outfit AhnLab.…
- Do you still need to pay for antivirus software in 2024?www.zdnet.com Do you still need to pay for antivirus software in 2024?
Landlines. Checkbooks. AM radio. Let's add third-party antivirus software to the list of things you can stop using.

Landlines. Checkbooks. AM radio. Let's add third-party antivirus software to the list of things you can stop using.
- Now The EU Council Should Finally Understand: No One Wants “Chat Control”www.eff.org Now The EU Council Should Finally Understand: No One Wants “Chat Control”
The EU Council has now passed a 4th term without passing its controversial message-scanning proposal. The just-concluded Belgian Presidency failed to broker a deal that would push forward this regulation, which has now been debated in the EU for more than two years. For all those who have reached...

The EU Council has now passed a 4th term without passing its controversial message-scanning proposal. The just-concluded Belgian Presidency failed to broker a deal that would push forward this regulation, which has now been debated in the EU for more than two years. For all those who have reached out to sign the “Don’t Scan Me” petition, thank you—your voice is being heard. News reports indicate the sponsors of this flawed proposal withdrew it because they couldn’t get a majority of member states to support it. Now, it’s time to stop attempting to compromise encryption in the name of public safety. EFF has opposed this legislation from the start. Today, we’ve published a statement, along with EU civil society groups, explaining why this flawed proposal should be withdrawn. The scanning proposal would create “detection orders” that allow for messages, files, and photos from hundreds of millions of users around the world to be compared to government databases of child abuse images. At some points during the debate, EU officials even suggested using AI to scan text conversations and predict who would engage in child abuse. That’s one of the reasons why some opponents have labeled the proposal “chat control.” There’s scant public support for government file-scanning systems that break encryption. Nor is there support in EU law. People who need secure communications the most—lawyers, journalists, human rights workers, political[...]
- Nasty regreSSHion bug in OpenSSH puts around 700K Linux boxes at riskgo.theregister.com Nasty regreSSHion bug affects around 700K Linux systems
Full system takeovers on the cards, for those with enough patience to pull it off

Full system takeovers on the cards, for those with enough patience to pull it off Glibc-based Linux systems are vulnerable to a new bug (CVE-2024-6387) in OpenSSH's server (sshd) and should upgrade to the latest version.…
- OpenSSH 9.8p1
This is a Linux/portable port of OpenBSD's excellent OpenSSH. OpenSSH is based on the last free version of Tatu Ylonen's SSH with all patent-encumbered algorithms removed, all known security bugs fixed, new features reintroduced, and many other clean-ups.
- IBM Consulting partners with Microsoft to help clients modernize security operationswww.helpnetsecurity.com IBM Consulting partners with Microsoft to help clients modernize security operations - Help Net Security
IBM Consulting and Microsoft collaborate to help clients modernize security operations and protect against cloud identity threats.

IBM Consulting and Microsoft announce strengthened cybersecurity collaboration to help clients simplify and modernize their security operations, and manage and protect their hybrid cloud identities. As organizations embrace hybrid cloud and AI to drive innovation, they require advanced security capabilities to protect their most valuable data. By combining IBM Consulting’s cybersecurity services with Microsoft’s comprehensive security technology portfolio, the two companies are providing clients the tools and expertise needed to help them simplify and modernize … More → The post IBM Consulting partners with Microsoft to help clients modernize security operations appeared first on Help Net Security.
- New Skimmer Malware Attacking E-commerce WebSites To Steal Credit Card Data
Researchers identified a new variant of credit card skimming attack, the Caesar Cipher Skimmer, targeting multiple content management systems (CMS), including WordPress, Magento, and OpenCart.  The skimmer specifically targets the checkout process, injecting malicious code into the checkout PHP file, as the attack leverages obfuscated strings and a Caesar Cipher technique to hide its malicious […] The post New Skimmer Malware Attacking E-commerce WebSites To Steal Credit Card Data appeared first on Cyber Security News.
- Quantum is unimportant to post-quantumblog.trailofbits.com Quantum is unimportant to post-quantum
By Opal Wright You might be hearing a lot about post-quantum (PQ) cryptography lately, and it’s easy to wonder why it’s such a big deal when nobody has actually seen a quantum computer.…
Comments
- SEC tries to expand crypto jurisdiction with Consensys lawsuitprotos.com SEC tries to expand crypto jurisdiction with Consensys lawsuit
The SEC has filed a lawsuit against Consensys alleging its MetaMask swaps service makes it an unregistered broker.

The SEC has filed a lawsuit against Consensys alleging its MetaMask swaps service makes it an unregistered broker. The post SEC tries to expand crypto jurisdiction with Consensys lawsuit appeared first on Protos.
- The US finalizes rules requiring custodial crypto platforms to report user transaction info to the IRS; DeFi platforms are exempt amid fierce crypto lobbying (Paul Kiernan/Wall Street Journal)www.techmeme.com The US finalizes rules requiring custodial crypto platforms to report user transaction info to the IRS; DeFi platforms are exempt amid fierce crypto lobbying
By Paul Kiernan / Wall Street Journal. View the full context on Techmeme.

Paul Kiernan / Wall Street Journal: The US finalizes rules requiring custodial crypto platforms to report user transaction info to the IRS; DeFi platforms are exempt amid fierce crypto lobbying — Treasury finalizes rules to deter crypto tax evasion—but softens them after industry lobbying push
- Hackers exploit critical D-Link DIR-859 router flaw to steal passwordswww.bleepingcomputer.com Hackers exploit critical D-Link DIR-859 router flaw to steal passwords
Hackers are exploiting a critical vulnerability that affects all D-Link DIR-859 WiFi routers to collect account information from the device, including passwords.

Hackers are exploiting a critical vulnerability that affects all D-Link DIR-859 WiFi routers to collect account information from the device, including passwords. [...]
- Interpol Arrests Thousands in Crackdown on International Online Scamsgizmodo.com Interpol Arrests Thousands in Crackdown on International Online Scams
Americans lost $10 billion to fraud in 2023, with $1.4 billion worth starting on social media, according to the FTC.

Police around the world have arrested 3,950 people and seized assets totaling $257 million in a coordinated effort to crack down on online scams, according to a news release Thursday from Interpol. Dubbed Operation First Light 2024, the scammers engaged in a variety of online crimes, including phishing, investment…Read more...
- Microsoft hits snooze again on security certificate renewalgo.theregister.com Microsoft hits snooze again on security certificate renewal
Seeing weird warnings in Microsoft 365 and Office Online? That'll be why
Seeing weird warnings in Microsoft 365 and Office Online? That'll be why Microsoft has expiration issues with its TLS certificates, resulting in unwanted security warnings.…
- Microsoft’s AI boss thinks it’s perfectly OK to steal content if it’s on the open webwww.theverge.com Microsoft’s AI boss thinks it’s perfectly OK to steal content if it’s on the open web
That is not how fair use works.

Photo by Riccardo Savi/Getty Images for Concordia Summit
Microsoft AI boss Mustafa Suleyman incorrectly believes that the moment you publish anything on the open web, it becomes “freeware” that anyone can freely copy and use. When CNBC’s Andrew Ross Sorkin asked him whether “AI companies have effectively stolen the world’s IP,” he said: I think that with respect to content that’s already on the open web, the social contract of that content since the ‘90s has been that it is fair use. Anyone can copy it, recreate with it, reproduce with it. That has been “freeware,” if you like, that’s been the understanding.
Microsoft AI CEO Mustafa Suleyman: the social contract for content that is on the open web is that it's "freeware" for training AI models pic.twitter.com/FN1xrqnJC0— Tsarathustra...
Continue reading…
- Microsoft Tells Texas Agencies They Were Exposed in Russian Hackwww.bloomberg.com Microsoft Tells Texas Agencies They Were Exposed in Russian Hack
Microsoft Corp. has told more than a dozen state agencies and public universities in Texas that Russian state-sponsored hackers accessed emails between them and the software giant.
Microsoft Corp. has told more than a dozen state agencies and public universities in Texas that Russian state-sponsored hackers accessed emails between them and the software giant.
- Inside a violent gang’s ruthless crypto-stealing home invasion spreearstechnica.com Inside a violent gang’s ruthless crypto-stealing home invasion spree
More than a dozen men threatened, assaulted, tortured, or kidnapped 11 victims.

More than a dozen men threatened, assaulted, tortured, or kidnapped 11 victims.
- Microsoft AI CEO Mustafa Suleyman says content on the open web is "freeware" that anyone can copy or use to reproduce, due to the fair use "social contract" (Sean Endicott/Windows Central)www.techmeme.com Microsoft AI CEO Mustafa Suleyman says content on the open web is “freeware” that anyone can copy or use to reproduce, due to the fair use “social contract”
By Sean Endicott / Windows Central. View the full context on Techmeme.

Sean Endicott / Windows Central: Microsoft AI CEO Mustafa Suleyman says content on the open web is “freeware” that anyone can copy or use to reproduce, due to the fair use “social contract” — Microsoft's CEO of AI said that content on the open web can be copied and used to create new content.
- Don't Forget to Report a Breach: A Cautionary Talewww.darkreading.com Don't Forget to Report a Breach: A Cautionary Tale
Responding to an incident quickly is important, but it shouldn't come at the expense of reporting it to the appropriate regulatory bodies.

Responding to an incident quickly is important, but it shouldn't come at the expense of reporting it to the appropriate regulatory bodies.
- Web scraping is not just a security or fraud problemwww.helpnetsecurity.com Web scraping is not just a security or fraud problem - Help Net Security
Web scraping is not just a fraud or security problem, it is also a business problem. Web scraping is commonly used by ecommerce businesses.

Bots compose 42% of overall web traffic, and 65% of these bots are malicious, according to Akamai. Negative effects of scraper bots on business operations Web scraping is not just a fraud or security problem, it is also a business problem. Scraper bots have a negative effect on many facets of the organization, including revenue, competitive edge, brand identity, customer experience, infrastructure costs, and digital experience. With its reliance on revenue-generating web applications, the ecommerce … More → The post Web scraping is not just a security or fraud problem appeared first on Help Net Security.
- Polyfill.io, BootCDN, Bootcss, Staticfile attack traced to 1 operatorwww.bleepingcomputer.com Polyfill.io, BootCDN, Bootcss, Staticfile attack traced to 1 operator
The recent large scale supply chain attack conducted via multiple CDNs, namely Polyfill.io, BootCDN, Bootcss, and Staticfile that affected up to tens of millions of websites has been traced to a common operator. Researchers discovered a public GitHub repository with leaked API keys helping them dra...

The recent large scale supply chain attack conducted via multiple CDNs, namely Polyfill.io, BootCDN, Bootcss, and Staticfile that affected up to tens of millions of websites has been traced to a common operator. Researchers discovered a public GitHub repository with leaked API keys helping them draw a conclusion. [...]
- The Importance of Cyber Threat Intelligence: Insights from Recent Nobelium Attackswww.sans.org The Importance of Cyber Threat Intelligence: Insights from Recent Nobelium Attacks
A blog underscoring the importance of cyber threat intelligence in reference to the recent Nobelium attacks
A blog underscoring the importance of cyber threat intelligence in reference to the recent Nobelium attacks
- WA man set up fake free wifi at Australian airports and on flights to steal people’s data, police allegewww.theguardian.com WA man set up fake free wifi at Australian airports and on flights to steal people’s data, police allege
Investigation launched after airline reported a suspicious network popped up during a domestic flight in April

Investigation launched after airline reported a suspicious network popped up during a domestic flight in AprilFollow our Australia news live blog for latest updatesGet our morning and afternoon news emails, free app or daily news podcastA man has been charged after he allegedly set up fake free wifi networks at Australian airports and on domestic flights to steal personal data from unsuspecting members of the public.The 42-year-old Western Australian man is facing nine cybercrime charges and was due to appear in Perth magistrates court on Friday.Sign up for Guardian Australia’s free morning and afternoon email newsletters for your daily news roundup Continue reading...
- TeamViewer can't bring itself to say someone broke into its network – but it happenedgo.theregister.com TeamViewer responds to security 'irregularity' in IT network
Claims customer data, prod environment not affected as NCC sounds alarm
Claims customer data, prod environment not affected as NCC sounds alarm TeamViewer on Thursday said its security team just "detected an irregularity" within one of its networks – which is a fancy way of saying someone broke in.…
- Polyfill.io owner punches back at 'malicious defamation' amid domain shutdowngo.theregister.com Polyfill.io owner slams Cloudflare after domain shutdown
No supply-chain attacks to see over here!

No supply-chain attacks to see over here! After having its website shut down, the polyfill.io owner is fighting back against claims it smuggled suspicious code onto websites all across the internet.…
- CISOs becoming more comfortable with risk levelswww.helpnetsecurity.com CISOs becoming more comfortable with risk levels - Help Net Security
Contradicting legacy stereotypes of the CISO as inherently risk averse, only 16% of CISOs classified their current risk appetite as low.

Shifts in the cyber threats landscape have changed the way today’s CISOs evaluate their business’s risk appetite, according to Netskope. CISO risk appetite levels Specifically, 92% of CISOs report that these changes are creating tensions with their CEO and other members of the C-suite, and 66% say they are “walking a tightrope” between what the business wants and what makes sense from a security perspective. Contradicting legacy stereotypes of the CISO as inherently risk averse, … More → The post CISOs becoming more comfortable with risk levels appeared first on Help Net Security.
- Majority of Critical Open Source Projects Contain Memory Unsafe Codewww.infosecurity-magazine.com Majority of Critical Open Source Projects Contain Memory Unsafe Code
A CISA analysis in collaboration with international partners concluded most critical open source projects potentially contain memory safety vulnerabilities

A CISA analysis in collaboration with international partners concluded most critical open source projects potentially contain memory safety vulnerabilities
- «Poseidon» Mac stealer distributed via Google adswww.malwarebytes.com 'Poseidon' Mac stealer distributed via Google ads | Malwarebytes
A competitor of the infamous Atomic Stealer targeting Mac users, has just launched a new campaign to lure in more victims.

A competitor of the infamous Atomic Stealer targeting Mac users, has just launched a new campaign to lure in more victims.
- Apple Patches AirPods Bluetooth Vulnerability That Could Allow Eavesdroppingthehackernews.com Apple Patches AirPods Bluetooth Vulnerability That Could Allow Eavesdropping
Apple releases critical security updates for AirPods and visionOS, addressing Bluetooth vulnerabilities and potential exploits in spatial computing.

Apple has released a firmware update for AirPods that could allow a malicious actor to gain access to the headphones in an unauthorized manner. Tracked as CVE-2024-27867, the authentication issue affects AirPods (2nd generation and later), AirPods Pro (all models), AirPods Max, Powerbeats Pro, and Beats Fit Pro. "When your headphones are seeking a connection request to one of your previously
- Multiple vulnerabilities in TP-Link Omada system could lead to root accessblog.talosintelligence.com Multiple vulnerabilities in TP-Link Omada system could lead to root access
Affected devices could include wireless access points, routers, switches and VPNs.
Affected devices could include wireless access points, routers, switches and VPNs.
- Researchers in Rabbit R1's jailbreaking community say Rabbit left critical API keys hardcoded in its code, which would let hackers use Rabbit's internal systems (Jason Koebler/404 Media)www.techmeme.com Researchers in Rabbit R1's jailbreaking community say Rabbit left critical API keys hardcoded in its code, which would let hackers use Rabbit's internal systems
By Jason Koebler / 404 Media. View the full context on Techmeme.

Jason Koebler / 404 Media: Researchers in Rabbit R1's jailbreaking community say Rabbit left critical API keys hardcoded in its code, which would let hackers use Rabbit's internal systems — Members of a community focused on jailbreaking and reverse engineering the Rabbit R1 AI assistant device say that Rabbit left …