AMD "INCEPTION" CPU Vulnerability Disclosed
AMD "INCEPTION" CPU Vulnerability Disclosed

www.phoronix.com
AMD "INCEPTION" CPU Vulnerability Disclosed

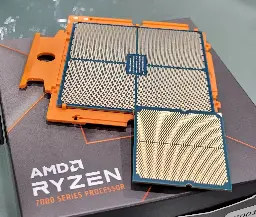
AMD-SB-7005 "Return Address Security Bulletin" outlines this new speculative side channel attack affecting recent EPYC and Ryzen processors.
AMD has received an external report titled ‘INCEPTION’, describing a new speculative side channel attack. AMD believes ‘Inception’ is only potentially exploitable locally, such as via downloaded malware, and recommends customers employ security best practices, including running up-to-date software and malware detection tools. AMD is not aware of any exploit of ‘Inception’ outside the research environment, at this time.