
Cybersecurity
- Boeing confirms attempted $200 million ransomware extortion attemptcyberscoop.com Boeing confirms attempted $200 million ransomware extortion attempt
That attempt was one of multiple “extremely large” ransom demands made by LockBit over the years, authorities said.

- Actor IntelBroker is selling data from Europol in Breachforumsbreachforums.st Europol Data Breach | BreachForums
Hello BreachForums Community,Today, I am selling the entire data breach belonging to Europol. Thank...
Data offered include Alliance employees, FOUO source code, PDFs, Documents for recon and guidelines.
- Citrix warns admins to manually mitigate PuTTY SSH client bugwww.bleepingcomputer.com Citrix warns admins to manually mitigate PuTTY SSH client bug
Citrix notified customers this week to manually mitigate a PuTTY SSH client vulnerability that could allow attackers to steal a XenCenter admin's private SSH key.

- IntelBroker Hacker Leaks Alleged HSBC & Barclays Bank Datawww.hackread.com IntelBroker Hacker Leaks Alleged HSBC & Barclays Bank Data
Follow us on Twitter (X) @Hackread - Facebook @ /Hackread

- Proton VPN TunnelVision support response.
I contacted Proton VPN about the TunnelVision exploit and I got a response. I feel great about it, thank you Proton!
>Hi, > > >Thank you for your patience. > > >Our engineers have conducted a thorough analysis of this threat, reconstructed it experimentally, and tested it on Proton VPN. Please note that the attack can only be carried out if the local network itself is compromised. > > >Regardless, we're working on a fix for our Linux application that will provide full protection against it, and it'll be released as soon as possible. > > >If there's anything else that I can help you with in the meantime, please feel free to let me know. > > >Have a nice day!
- New Spectre-Style 'Pathfinder' Attack Targets Intel CPU, Leak Encryption Keys and Datathehackernews.com New Spectre-Style 'Pathfinder' Attack Targets Intel CPU, Leak Encryption Keys and Data
Researchers have uncovered a new class of attacks called Pathfinder that can extract encryption keys and sensitive data from Intel CPUs.

- Hijack Loader Malware Employs Process Hollowing, UAC Bypass in Latest Versionthehackernews.com Hijack Loader Malware Employs Process Hollowing, UAC Bypass in Latest Version
A newer version of the Hijack Loader malware has been observed with updated anti-analysis techniques to evade detection.

- Zscaler takes "test environment" offline after rumors of a breachwww.bleepingcomputer.com Zscaler takes "test environment" offline after rumors of a breach
Zscaler says that they discovered an exposed "test environment" that was taken offline for analysis after rumors circulated that a threat actor was selling access to the company's systems.

- Change Healthcare went without cyber insurance before debilitating ransomware attackwww.csoonline.com Change Healthcare went without cyber insurance before debilitating ransomware attack
Organizations that eschew cyber insurance give up not only financial protection but also advice from the insurer on improving the security of their systems.

> Organizations that eschew cyber insurance give up not only financial protection but also advice from the insurer on improving the security of their systems.
- BetterHelp to pay $7.8 million to 800,000 in health data sharing settlementwww.bleepingcomputer.com BetterHelp to pay $7.8 million to 800,000 in health data sharing settlement
BetterHelp has agreed to pay $7.8 million in a settlement agreement with the U.S. Federal Trade Commission (FTC) over allegations of misusing and sharing consumer health data for advertising purposes.

> BetterHelp has agreed to pay $7.8 million in a settlement agreement with the U.S. Federal Trade Commission (FTC) over allegations of misusing and sharing consumer health data for advertising purposes.
- Security company exposes 1.2M guard and suspect recordswww.theregister.com Security company exposes 1.2M guard and suspect records
Thousands of ID cards plus CCTV snaps of suspects found online

- Chinese Hackers Deployed Backdoor Quintet to Down MITREwww.darkreading.com Chinese Hackers Deployed Backdoor Quintet to Down MITRE
MITRE's hackers made use of at least five different Web shells and backdoors as part of their attack chain.

- UK confirms Ministry of Defence payroll data exposed in data breachwww.bleepingcomputer.com UK confirms Ministry of Defence payroll data exposed in data breach
The UK Government confirmed today that a threat actor recently breached the country's Ministry of Defence and gained access to part of the Armed Forces payment network.

- Analyzing the vulnerability landscape in Q1 2024securelist.com Analyzing the vulnerability landscape in Q1 2024
The report provides vulnerability and exploit statistics, key trends, and analysis of interesting vulnerabilities discovered in Q1 2024.

Kaspersky's report highlights a steady increase in software vulnerabilities, with a surge in critical ones due to factors like bug bounty programs and complex software. Exploits, especially those available publicly, pose significant threats, and their numbers are rising. Key vulnerabilities in Q1 2024 include those affecting XZ, Visual Studio, runc, ScreenConnect, Windows Defender, and TeamCity.
- Critical vulnerabilities in BIG-IP appliances leave big networks open to intrusionarstechnica.com Critical vulnerabilities in BIG-IP appliances leave big networks open to intrusion
Hackers can exploit them to gain full administrative control of internal devices.

> Hackers can exploit them to gain full administrative control of internal devices.
- Kinsing crypto mining campaign targets 75 cloud-native applicationswww.csoonline.com Kinsing crypto mining campaign targets 75 cloud-native applications
Five years after being discovered, the Kinsing cryptojacking operation remains very active against organizations, employing daily probes for vulnerable applications using an ever-growing list of exploits.

> Five years after being discovered, the Kinsing cryptojacking operation remains very active against organizations, employing daily probes for vulnerable applications using an ever-growing list of exploits.
- CHM Malware Stealing User Information Being Distributed in Koreaasec.ahnlab.com CHM Malware Stealing User Information Being Distributed in Korea - ASEC BLOG
AhnLab SEcurity intelligence Center (ASEC) has recently discovered circumstances of a CHM malware strain that steals user information being distributed to Korean users. The distributed CHM is a type that has been constantly distributed in various formats such as LNK, DOC, and OneNote from the past. ...

- LockBit ransomware admin identified, sanctioned in US, UK, Australiawww.bleepingcomputer.com LockBit ransomware admin identified, sanctioned in US, UK, Australia
The FBI, UK National Crime Agency, and Europol have unveiled sweeping indictments and sanctions against the admin of the LockBit ransomware operation, with the identity of the Russian threat actor revealed for the first time.

> The FBI, UK National Crime Agency, and Europol have unveiled sweeping indictments and sanctions against the admin of the LockBit ransomware operation, with the identity of the Russian threat actor revealed for the first time.
- Over 50,000 Tinyproxy servers vulnerable to critical RCE flawwww.bleepingcomputer.com Over 50,000 Tinyproxy servers vulnerable to critical RCE flaw
Nearly 52,000 internet-exposed Tinyproxy instances are vulnerable to CVE-2023-49606, a recently disclosed critical remote code execution (RCE) flaw.

> Nearly 52,000 internet-exposed Tinyproxy instances are vulnerable to CVE-2023-49606, a recently disclosed critical remote code execution (RCE) flaw.
- Nearly 184,000 MedStar Health patients' personal data possibly breachedtherecord.media Nearly 184,000 MedStar Health patients' personal data possibly breached
The major Washington, D.C., and Maryland health network says the personal data of tens of thousands of people was likely exposed when an outsider accessed emails and files belonging to three employees.

- Hackers exploit LiteSpeed Cache flaw to create WordPress adminswww.bleepingcomputer.com Hackers exploit LiteSpeed Cache flaw to create WordPress admins
Hackers have been targeting WordPress sites with an outdated version of the LiteSpeed Cache plugin to create administrator users and gain control of the websites.

> Hackers have been targeting WordPress sites with an outdated version of the LiteSpeed Cache plugin to create administrator users and gain control of the websites.
- zEus Stealer Distributed via Crafted Minecraft Source Packwww.fortinet.com zEus Stealer Distributed via Crafted Minecraft Source Pack | FortiGuard Labs
FortiGuard Labs analysis of a zEus batch stealer distributed via a crafted Minecraft source pack. Learn more.…

- Stealing cookies: Researchers describe how to bypass modern authenticationcyberscoop.com Stealing cookies: Researchers describe how to bypass modern authentication
Passwordless authentication standards have improved identity security, but new research indicates this technology is vulnerable to token hijacks and man-in-the-middle attacks.
- 3D-Printed USB Dead Man Switch (Prototype Demo)www.buskill.in 3D-Printable BusKill Prototype Demo - BusKill
Demo of our DIY USB Dead Man Switch (prototype) with a 3D-Printable Case triggering a lockscreen when the kill-cord's connection is severed.

Today we're ecstatic to publish our first demo showing a homemade BusKill Cable (in the prototype 3D-printed case) triggering a lockscreen.
| [!3D-Printed USB Dead Man Switch (Prototype Demo)](https://www.buskill.in/3d-print-2024-05/) | |:--:| | Watch the 3D-Printed USB Dead Man Switch (Prototype Demo) for more info youtube.com/v/vFTQatw94VU |
In our last update, I showed a video demo where I successfully triggered a lockscreen using a BusKill prototype without the 3D-printed body for the case and N35 disc magnets. I realized that the N35 disc magnets were not strong enough. In this update, I show a demo with the prototype built inside a 3D-printed case and with (stronger) N42 and N52 cube magnets.
What is BusKill?
BusKill is a laptop kill-cord. It's a USB cable with a magnetic breakaway that you attach to your body and connect to your computer.
| [!What is BusKill? (Explainer Video)](https://www.buskill.in/#demo) | |:--:| | Watch the BusKill Explainer Video for more info youtube.com/v/qPwyoD_cQR4 |
If the connection between you to your computer is severed, then your device will lock, shutdown, or shred its encryption keys -- thus keeping your encrypted data safe from thieves that steal your device.
Why?
While we do what we can to allow at-risk folks to purchase BusKill cables anonymously, there is always the risk of interdiction.
We don't consider hologram stickers or tamper-evident tape/crisps/glitter to be sufficient solutions to supply-chain security. Rather, the solution to these attacks is to build open-source, easily inspectable hardware whose integrity can be validated without damaging the device and without sophisticated technology.
Actually, the best way to confirm the integrity of your hardware is to build it yourself. Fortunately, BusKill doesn't have any circuit boards, microcontrollers, or silicon; it's trivial to print your own BusKill cable -- which is essentially a USB extension cable with a magnetic breakaway in the middle
Mitigating interdiction via 3D printing is one of many reasons that Melanie Allen has been diligently working on prototyping a 3D-printable BusKill cable this year. In this article, we hope to showcase her progress and provide you with some OpenSCAD and
.stlfiles you can use to build your own version of the prototype, if you want to help us test and improve the design.Print BusKill
[!Photo of the 3D-Printed BusKill Prototype](https://www.buskill.in/3d-print-2024-05/)
If you'd like to reproduce our experiment and print your own BusKill cable prototype, you can download the stl files and read our instructions here:
Iterate with us!
If you have access to a 3D Printer, you have basic EE experience, or you'd like to help us test our 3D printable BusKill prototype, please let us know. The whole is greater than the sum of its parts, and we're eager to finish-off this 3D printable BusKill prototype to help make this security-critical tool accessible to more people world-wide!
- China-Linked Hackers Suspected in ArcaneDoor Cyberattacks Targeting Network Devicesthehackernews.com China-Linked Hackers Suspected in ArcaneDoor Cyberattacks Targeting Network Devices
New findings suggest the ArcaneDoor cyber espionage campaign targeting network devices from Cisco (CVE-2024-20353, CVE-2024-20359).

- Citrix Addresses High-Severity NetScaler Servers Flawwww.darkreading.com Citrix Addresses High-Severity NetScaler Servers Flaw
The flaw was nearly identical to last year's CitrixBleed flaw, but not as severe.

- Android bug leaks DNS queries even when VPN kill switch is enabledwww.bleepingcomputer.com Android bug leaks DNS queries even when VPN kill switch is enabled
A Mullvad VPN user has discovered that Android devices leak DNS queries when switching VPN servers even though the "Always-on VPN" feature was enabled with the "Block connections without VPN" option.

- CVE-2024-3661: TunnelVision - How Attackers Can Decloak Routing-Based VPNs For a Total VPN Leakwww.leviathansecurity.com CVE-2024-3661: TunnelVision - How Attackers Can Decloak Routing-Based VPNs For a Total VPN Leak — Leviathan Security Group - Penetration Testing, Security Assessment, Risk Advisory
We discovered a fundamental design problem in VPNs and we're calling it TunnelVision. This problem lets someone see what you're doing online, even if you think you're safely using a VPN.

- NVIDIA patches three ChatRTX security bugswww.scmagazine.com NVIDIA patches three ChatRTX security bugs
Security pros advise teams to use demo apps such as ChatRTX mainly in a test environment.

- Police resurrect LockBit's site and troll the ransomware gangtechcrunch.com Police resurrect LockBit's site and troll the ransomware gang | TechCrunch
An international coalition of police agencies have resurrected the dark web site of the notorious LockBit ransomware gang, which they had seized earlier

> An international coalition of police agencies have resurrected the dark web site of the notorious LockBit ransomware gang, which they had seized earlier
- Finland warns of Android malware attacks breaching bank accountswww.bleepingcomputer.com Finland warns of Android malware attacks breaching bank accounts
Finland's Transport and Communications Agency (Traficom) has issued a warning about an ongoing Android malware campaign targeting banking accounts.

- Russian GRU Hackers Compromised German, Czech Targetswww.bankinfosecurity.in Russian GRU Hackers Compromised German, Czech Targets
The German and Czech governments on Friday disclosed that Russian military intelligence hackers targeted political parties and critical infrastructure as part of an

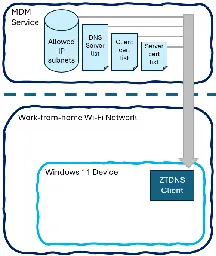
- Microsoft: Announcing Zero Trust DNS Private Previewtechcommunity.microsoft.com Announcing Zero Trust DNS Private Preview
Enabling domain-name-based lockdown of Windows for Zero Trust deployments in future versions of Windows
- Germany blames Fancy Bear for 2023 hacking campaignwww.theregister.com Germany blames Fancy Bear for 2023 hacking campaign
ALSO: Microsoft promises to git gud on cybersecurity; unqualified attackers are targeting your water systems, and more

- Amnesty International Cites Indonesia as a Spyware Hubwww.darkreading.com Amnesty International Cites Indonesia as a Spyware Hub
The growing amount of surveillance technology being deployed in the country is concerning due to Indonesia's increasing blows to civic rights.

- Iranian hackers pose as journalists to push backdoor malwarewww.bleepingcomputer.com Iranian hackers pose as journalists to push backdoor malware
The Iranian state-backed threat actor tracked as APT42 is employing social engineering attacks, including posing as journalists, to breach corporate networks and cloud environments of Western and Middle Eastern targets.
